









Deploying Windows Monthly Updates (without WSUS)
In connection with another article about Deploying Windows Updates via the Command Line, I have come to notice that it is not the end-all we thought it once was. With the Roll-Up Updates for Windows 7, 8.1, and 10, I have found a better way to deploy updates.


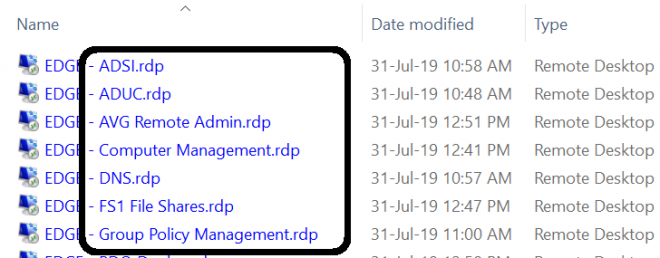
Add Network Clients, Protocols and Services via Command Line
In a previous post, I talked about why I couldn’t access any file shares, or connect remotely to some systems. The issue was caused by services, protocols and clients missing from the network adapters. Now that the issue had been identified, I had two choices: manually touch every machine, using the mouse for most of the work, or automate the process. This post describes the latter.


Creating an SSH Tunnel
So today, I was helping someone with a multi-site WordPress issue, and I linked to my blog. But guess what? It wasn’t coming up! All my external tests seemed to work, including Down for Everyone or Just Me, and even Cloudflare! I could still SSH into my server (as I was watching log files scroll by anyways!), so I knew it was up and accessible. So, what’s next?